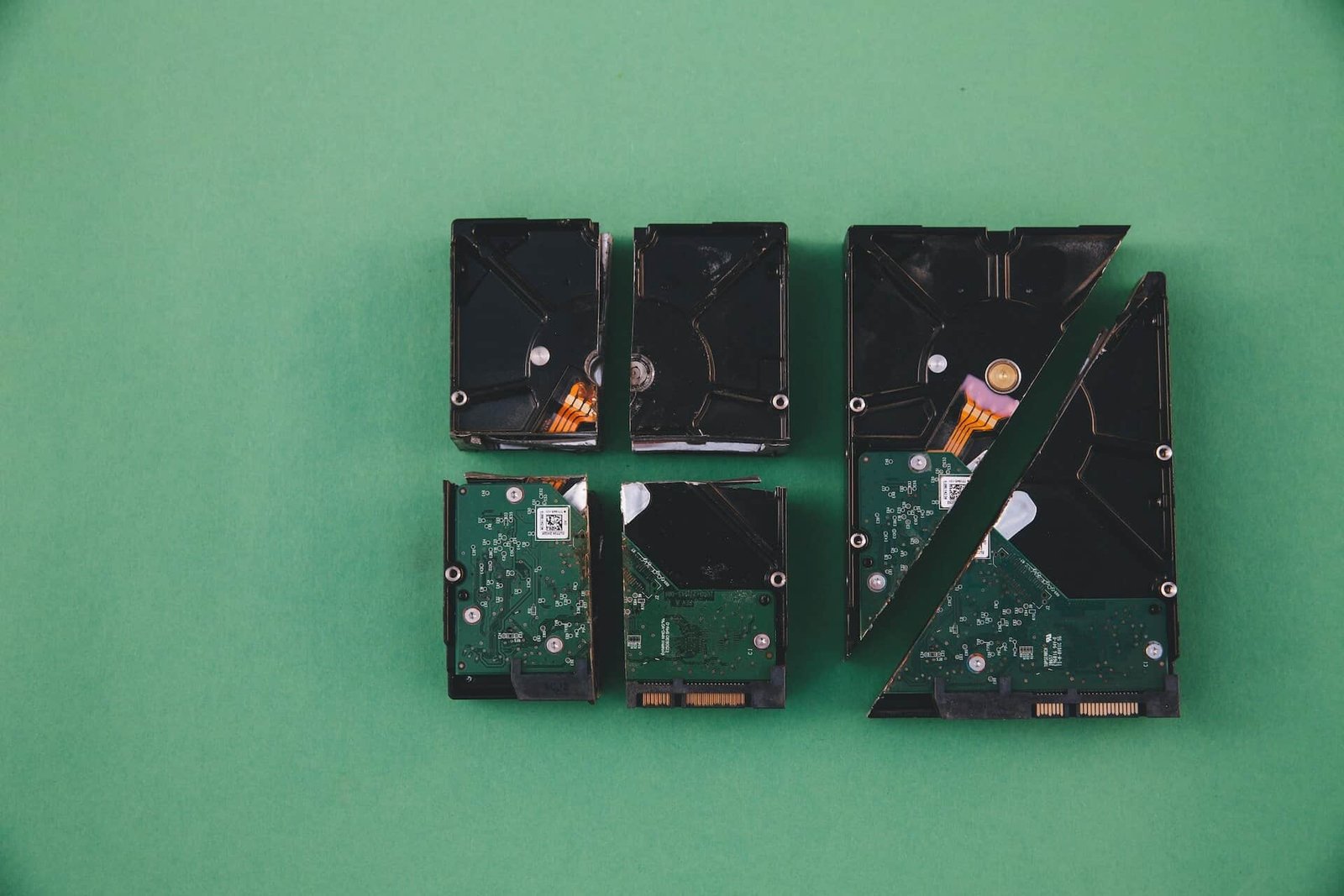
You have upgraded your computers. You have deleted the files, emptied the bin, maybe even done a factory reset. The devices are ready to go. The data is gone — right?
It is not. Not even close. This article explains why file deletion is not data destruction, what the actual risks are for Ghanaian businesses, and exactly what certified data destruction involves.
The Myth of the Delete Key
When you delete a file on any operating system, you are not removing the data. You are removing the pointer to the data — the entry in the file directory that tells the system where the file lives. The actual bytes remain on the storage medium, sitting quietly, until overwritten by new data.
On a hard drive with gigabytes of free space, those bytes can persist for months or years. Specialist data recovery software — available to anyone online for under $100 — can reconstruct deleted files with high fidelity.
| A factory reset on a phone or laptop does not wipe the data. It wipes the directory. Recovery tools can still find and extract the original files. |
This is not a theoretical risk. Researchers who have purchased second-hand hard drives in markets across West Africa have consistently found recoverable data — including financial records, customer databases, employee payroll information, login credentials, and sensitive communications — on drives that were believed by their previous owners to have been erased.
What Types of Data Are at Risk?
Think about every type of data that passes through a corporate device over its lifecycle. A laptop used by a bank employee for three years may contain:
- Customer account information and transaction records
- Internal financial models and forecasts
- Email correspondence including privileged or sensitive material
- Login credentials stored in browsers or password managers
- VPN configurations and network access details
- HR data including salaries, performance reviews, and personal information
- Client contracts and commercially sensitive documents
On a decommissioned server, multiply that by every user who ever accessed the system. On a mobile phone used by a senior executive, add authentication apps, messaging data, and location history.
The Legal Dimension in Ghana
Ghana’s Data Protection Act 2012 places a positive obligation on data controllers to ensure that personal data is protected from unauthorised access, accidental loss, and unlawful processing — including during the disposal of equipment that holds that data.
The Act does not specify technical methods, but the standard of care expected is what a reasonable, prudent organisation would apply. “We deleted the files” does not meet that standard. “We used a certified data destruction service and hold the certificate” does.
| The question regulators and auditors will ask is not whether you intended to protect the data. It is whether you took reasonable technical steps to do so. Certified destruction is the defensible answer. |
The Three Methods of Certified Data Destruction
There are three standard methods of data destruction, each appropriate to different situations and equipment types.
- Secure Data Overwriting (Software-Based Erasure) Specialist software overwrites every sector of the storage medium with random data — typically in multiple passes. When done correctly to recognised standards, this makes original data unrecoverable by any known method. This method is appropriate for hard drives and SSDs that are still functional and will be reused or donated. A certificate of erasure is generated electronically, recording the device serial number, erasure standard applied, and date.
- Physical Degaussing A degausser generates a powerful magnetic field that disrupts and randomises the magnetic domains on a hard drive platter, rendering the data unreadable. This method destroys the drive — it cannot be reused after degaussing — but is highly effective for magnetic media. It is often used alongside physical destruction for maximum security on sensitive devices.
- Physical Destruction The storage medium is physically shredded, crushed, or drilled. This is the definitive method for maximum-security environments or for devices where the data is so sensitive that no residual risk can be accepted. Hard drive shredding reduces platters to fragments of a few millimetres. A destruction certificate is issued recording the device and method. The resulting material then enters the recycling stream for material recovery.
What to Ask Your E-Waste Provider
Not all e-waste collectors offer genuine data destruction. When evaluating a provider, ask these specific questions:
- What data destruction standard do you apply — and can you show the accreditation?
- Do you issue a serial-number-level certificate of destruction for each device?
- Is destruction performed on-site at collection, or at a separate facility?
- Can you provide an unbroken chain-of-custody record from our premises to destruction?
- For physical destruction — how are the resulting fragments handled, and is there downstream documentation?
A provider that cannot answer these questions with confidence and specifics is not providing certified data destruction — regardless of what they call it.
Building a Data Destruction Policy
For organisations that regularly retire IT equipment, a documented data destruction policy is both a legal best practice and an operational necessity. A basic policy should cover:
- Which categories of device require certified destruction (all storage media, or specific classifications)
- The approved destruction method by device type
- The documentation that must be obtained and retained
- The record-keeping period (typically a minimum of three years)
- The authorised supplier(s) for data destruction services
Having a policy also demonstrates organisational intent if a data protection incident is ever investigated — it is evidence that the organisation took its obligations seriously.
| “Deleted” is not the same as “destroyed.” Only a destruction certificate proves the data is gone. |
| Protect your organisation with certified data destruction. → Request a Data Destruction Service |